It has been revealed weaknesses in the bank’s mobile applications left the door open for cybercriminals to take customers” money. Worse still, the bank was”forewarned by security experts of this weakness prior to the attack. So”how did the Tesco Bank hack come to be and what can we learn from it?
It was the largest ever cyber-attacks on a UK bank. One of the most significant things about the Tesco Bank hack was that customer accounts were penetrated forcefully without any credentials, which hasn’t happened before. Cybercriminals broke into Tesco Bank’s computer system and stole £2.5 m”from the current accounts of 9,000 customers.
The result of this attack was the scenario many people are afraid of waking up one morning and finding your bank account empty. Tesco had a responsibility to protect its customers and, by not listening to?penetration testers aboutA possible Tesco Bank“hack, causedAn erosion of trust.
It’s clear the companyeither wasn?t aware of the potential scale of the attack or it simply wasn?t equipped to deal with a cyber-attack at this level. In a moment of malicious compromise, Tesco should have had the appropriate detection and remediation protocols in place to stop the hackers before they could remove actual money from customer accounts.
Keeping pace with multiple threat vectors
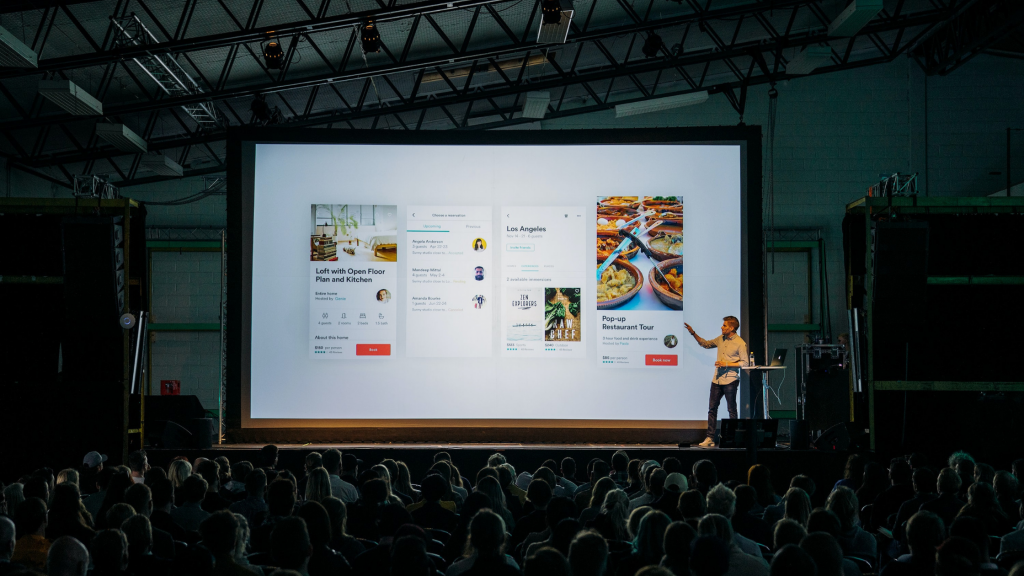
With the increasing number of connected devices for cybercriminals to exploit, there are more threat vectors for companies to protect. It has never been so easy to obtain confidential information. With the proliferation of mobile devices, social media and social engineering, there are now over a million ways to reach an individual and gain the keys to the kingdom. Platform firewalls can easily be misconfigured, creating backdoors for hackers to find vulnerabilities and exploit them. The more complex the network, the greater the likelihood they will make it in undetected.
The edgeless perimeter
Risks are increasingly extending beyond the perimeter to the individual user via social engineering. We have already seen compromised chip sets, backdoors in operating systems, and rogue apps placing malware on the device. The greatest element of concern in 2017 is how expanded attack vectors allow for lateral movement, with the bad guys looking to utilise mobile platforms as a means of gaining access to the core of the network.
While the Tesco Bank hack?will elevate security further towards being thought of as a high ticket item, many are left questioning how the industry will act together to resolve the issue. Like the Heartland breach in America in 2015, the company thought it was fully compliant and was still compromised, resulting in a year-long rehabilitation campaign. Instead, we should be asking what the industry is doing wrong” The industry at large has not embraced the notion of hyper-connectivity, which means users and clients alike are all individual vectors of threat.
Mobile platforms must be treated as an extension of the network
Securing devices and the traffic they create needs to be treated in the same way you would treat devices within the traditional network perimeter. Just like locking your doors every time you leave the house, you would never set up a network without a firewall but firewalls are no longer enough to protect the ‘edgeless perimeter’.
What happened to Tesco could happen to any company, of any size, in any sector
Financial services are accustomed to being in their own seemingly secure bubble. Now, however, that bubble has well and truly burst. Devices connected to each other via not only mobile networks but the Internet of Things has expanded the risk to all customer devices becoming compromised or attacked. The financial services industry has a great responsibility to safeguard people’s money and it is heavily regulated because of this. It is imperative, therefore, that it goes further than just basic blocking and tackling of threats within the firewall to encompass the new attack vectors associated with the myriad of connected devices.
Kirsten Bayis president and CEO of Cyber adAPT
Image: Shutterstock