Using the cloud to store data and as a means of gaining access to software, services and computing power has become business as usual for most businesses today. Thanks to the convenience of these offerings, and the significant reductions in the time and cost associated with installing and managing those resources locally, more than eight in every 10 UK small and medium businesses are using cloud services already and a third plan to invest further in the cloud this year.
It can be tempting to jump straight in and take advantage of this technology, but it’s important that organisations take some time to consider their needs, the types of data they?ll be entrusting to their cloud solution and the security requirements that come with this. The following four steps will help you choose and implement a solution that strikes this balance:
1. Determining your choice of cloud

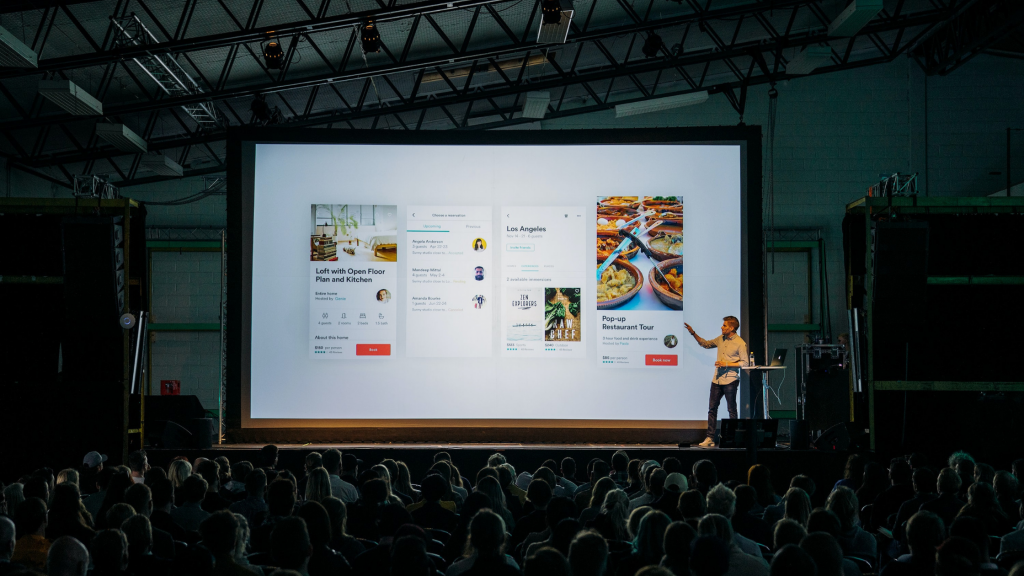
One of the most significant decisions to make is around the type of cloud that best suits your business. A public cloud from the likes of Amazon, Microsoft, Google or Dropbox tends to be the least expensive option since it only involves paying for a single service package.
That cost saving comes with a lower level of control, you will not be able to specify precisely how your data is protected, and most businesses using these services have no idea where their files are located.
Colocating one’s own IT equipment in a shared data centre may get around this issue as it allows businesses to control their security, replication and backup end-to-end, in effect creating their own private cloud.
The choice of cloud solution will depend on the business activities required and the sensitivity of the data that will be stored, many businesses opt for a mix of private and public cloud solutions to maximise the benefits of both.
2. Choosing connectivity that takes the strain
The rise of the cloud has already prompted many organisations to review their connectivity needs. In the last three years, we’ve seen the use of broadband connectivity halve among small and medium-sized businesses in favour of higher capacity services such as Ethernet leased lines that can handle the data strain created by the cloud.
3. Deciding on the data you’re confident to place in the cloud

Traditional approaches to cybersecurity involve placing a protective shield around a business and its on-premise IT systems and using tools such as firewalls to check files as they enter and leave the network.
Cloud computing has blurred these boundaries. Businesses are trusting more and more of their data and IT applications to third-party providers and their people are doing more business than ever outside of the office – working from home, at client premises and on the move via their mobile devices. Addressing this shift requires careful consideration.
4. Securing the cloud

With more business data located outside the company firewall, it becomes more important to secure that data, and not simply the network. There are various approaches that can be combined to help secure the data you entrust to the cloud:
Good password practice
One of the easiest things companies can do is insist on strong passwords as standard. Create a policy where passwords used for work should always be separate from any used personally at home.
Traditionally, the strongest passwords have included letters, numbers, and symbols to minimise the chances that they can be cracked by a bot, but there is a move now to encourage employees to create passwords based on three random words.
Multi-factor authentication
Strong passwords should be used as part of multifactor authentication, which maximises system resilience by granting access to users only after presenting several pieces of information. We ve helped clients establish robust multi-factor authentication protocols involving strong passwords, approved devices and physical tokens to help protect their cloud-based systems.
Appropriate encryption
Cybersecurity experts recommend that data in the cloud should be encrypted where it is stored, but also while it is in motion across the internet. Ensure websites you navigate are using HTTPS, this ensures your traffic is encrypted and cannot be intercepted.
Access to cloud applications
A lot of organisations using cloud services are also using Active Directory services located on their premises or in rented rack space in data centres to identify, authenticate and authorise access to cloud applications. This provides a greater element of control over the cloud environment, but it still relies on the business to keep their security controls fully up to date when a member of staff leaves the organisation.
Good people
Finally, while there is a lot that companies can do with technology to protect their cloud deployments, good recruitment and management practices are just as important. People need to be vetted before they are employed and regularly trained on how to avoid the main cybersecurity risks they might be exposed to.